24/7 SOC · MDR · Incident Response
Your SOC Team
Around the Clock From Day One
Enterprise defense, without the enterprise price tag. The average breach goes undetected for 204 days. Our SOC catches it in minutes.
Under attack right now? Call 949-438-8364
Official Partner · Exclusive Access
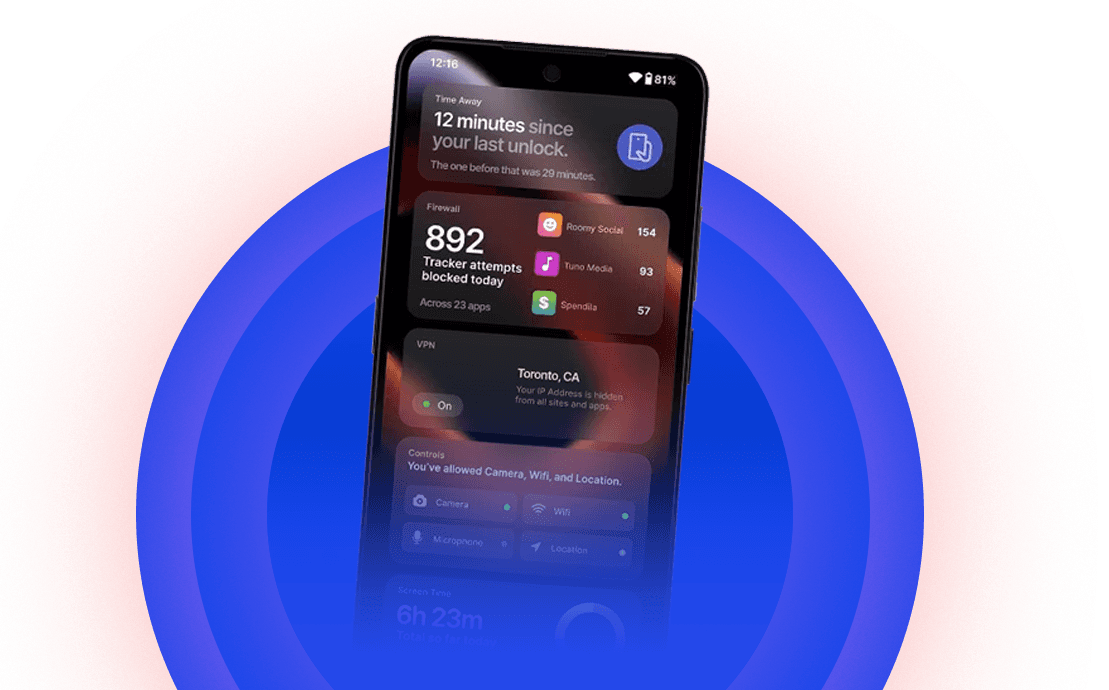
Take back control with The UP Phone by Unplugged
A smartphone designed from the ground up to safeguard your privacy: hardware kill-switch, built-in no-logs VPN, on-device firewall, and a Google-free operating system.
- Hardware kill-switch physically disconnects the battery
- Built-in no-logs VPN and on-device firewall
- Google-free OS with full app freedom
- Use code CODE4 for an exclusive discount
Official Partner · Exclusive Access
Private communications with SekurPrivate
Swiss-hosted encrypted email and messaging that doesn't sell your data, doesn't read your messages, and doesn't keep metadata.
- Zero-knowledge architecture — Sekur can't read your messages
- SwissProtocol encryption hosted on Swiss servers
- Anonymous account creation supported
- HIPAA-friendly for healthcare communication

● What we do
Enterprise defense.
Without the enterprise price tag.
Everything you need to detect, respond, and recover — operated by humans, not just dashboards.
Powered by Elastic Kibana
Every log, every alert, every signal — in one place.
We deploy and operate Elastic Kibana as the analytics backbone of your SOC — turning terabytes of telemetry into actionable detections, dashboards, and audit-ready reports.
- Real-time SIEM dashboards tuned to your environment
- Detection-as-code with version-controlled rules
- Compliance-grade log retention (SOC 2, HIPAA, PCI)
- Threat hunting queries built by senior analysts
rule "lateral_movement_smb" {
when event.action == "smb_connection"
and source.ip in internal_subnets
and destination.port == 445
severity: "high"
notify: soc@code4
}Our partners
Trusted Partners
Operating with — and trusted by — the platforms that power modern security.




Industries we protect
Defending teams across regulated sectors.
From HIPAA to PCI DSS to CMMC — we know the controls, the auditors, and the threats your sector faces.
Why choose us
Why businesses choose Code4 over building their own SOC.
Senior analysts, not just dashboards
Every alert is triaged by a human with experience — not auto-closed by a tool.
Live in two weeks, not two years
Onboarding measured in days, not the 12–18 months it takes to build in-house.
Predictable, flat-fee pricing
No per-event surprises, no per-GB shock bills. One transparent monthly cost.
1000+ incidents contained
Playbooks built from real-world response, not theoretical scenarios.
0 client breaches
Across the firm's history. Every client. Every year.
Compliance-ready from day one
SOC 2, HIPAA, PCI DSS, CMMC — evidence collected continuously, not at audit time.
● Testimonials
Trusted by the people responsible.
"Code4's SOC caught a credential-stuffing campaign at 3am that our previous MSSP missed for two days. They had the impacted accounts locked within 12 minutes."
"HIPAA compliance went from a binder we dusted off once a year to something our engineering team actually trusts. The Code4 team explains controls in language clinicians and auditors both accept."
"We tried building this in-house. Two analysts, a SIEM that never got tuned, and an inbox full of alerts no one had time to read. Code4 replaced all of that — for less than one analyst's salary."
Your Move. Before It's Theirs.
Talk to a senior analyst. No sales pitch. Just clarity on where you stand and what to do next.